Breadcrumb
Optimal Proportional Integral Derivative (PID) Controller Design for Smart Irrigation Mobile Robot with Soil Moisture Sensor
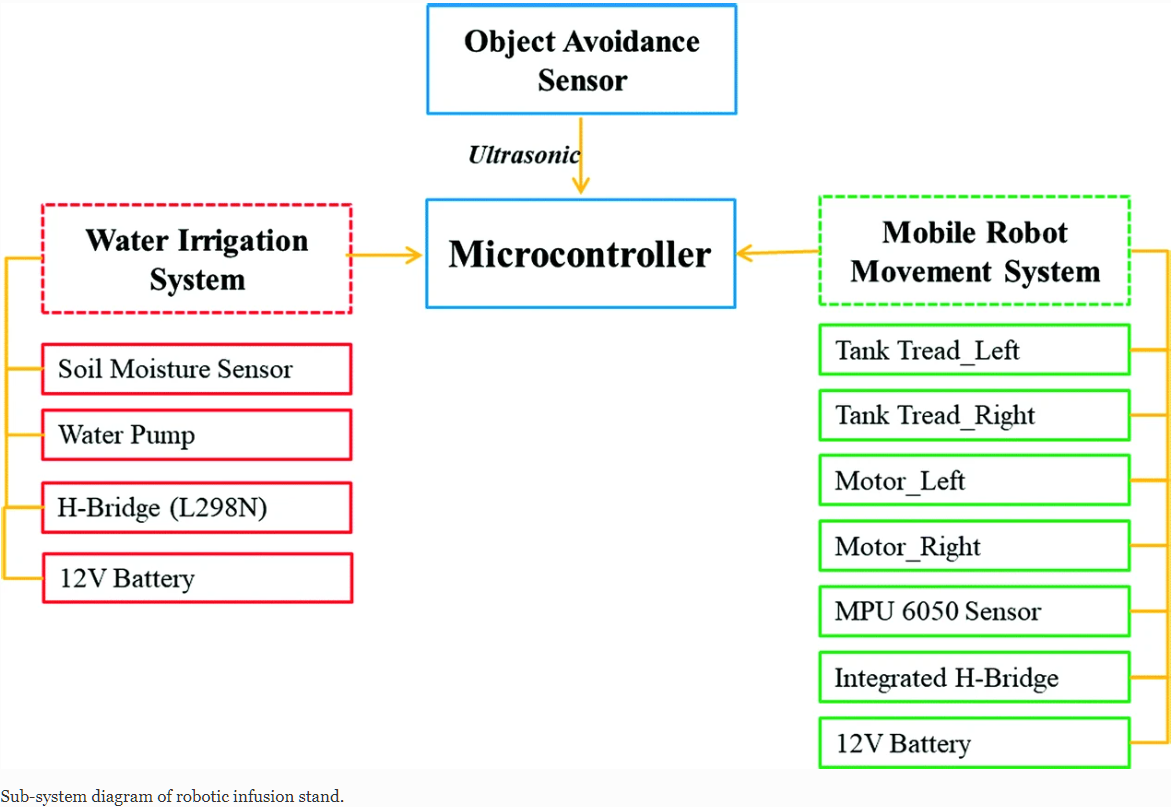
Uncertainty on the condition of the weather always give a major headache to the agricultural industry as the cultivated plant that is grown on a large scale commercially rely on the condition of the weather. Therefore, to reduce the interdependency on the weather itself, a recommendation to develop a prototypic mobile robot for smart irrigation is submitted. Smart irrigation system is an essential tool from yield point of view and scarcity of the water. This smart irrigation system adopts a soil moisture sensor to measure the moisture content of the soil and automatically provide a signal to
Improved memristor-based relaxation oscillator
This paper presents an improved memristor-based relaxation oscillator which offers higher frequency and wider tunning range than the existing reactance-less oscillators. It also has the capability of operating on two positive supplies or alternatively a positive and negative supply. Furthermore, it has the advantage that it can be fully integrated on-chip providing an area-efficient solution. On the other hand, The oscillation concept is discussed then a complete mathematical analysis of the proposed oscillator is introduced. Furthermore, the power consumption of the new relaxation circuit is
Improved spectrum mobility using virtual reservation in collaborative cognitive radio networks
Cognitive radio technology would enable a set of secondary users (SU) to opportunistically use the spectrum licensed to a primary user (PU). On the appearance of this PU on a specific frequency band, any SU occupying this band should free it for PUs. Typically, SUs may collaborate to reduce the impact of cognitive users on the primary network and to improve the performance of the SUs. In this paper, we propose and analyze the performance of virtual reservation in collaborative cognitive networks. Virtual reservation is a novel link maintenance strategy that aims to maximize the throughput of
Indoor localization and movement prediction algorithms with light-fidelity
Indoor localization has recently attended an increase in interest due to the potential for a wide range of services. In this paper, indoor high-precision positioning and motion prediction algorithms are proposed by using light fidelity (LI-FI) system with angular diversity receiver (ADR). The positioning algorithm uses to estimate the location of an object in the room. Furthermore, the prediction algorithm applies to predict the motion of that object. The simulation results show that the average root mean squares error of the positioning algorithm is about 0.6 cm, and the standard deviation
Fractional canny edge detection for biomedical applications
This paper presents a comparative study of edge detection algorithms based on integer and fractional order differentiation. A performance comparison of the two algorithms has been proposed. Then, a soft computing technique has been applied to both algorithms for better edge detection. From the simulations, it shows that better performance is obtained compared to the classical approach. The noise performances of those algorithms are analyzed upon the addition of random Gaussian noise, as well as the addition of salt and pepper noise. The performance has been compared to peak signal to noise
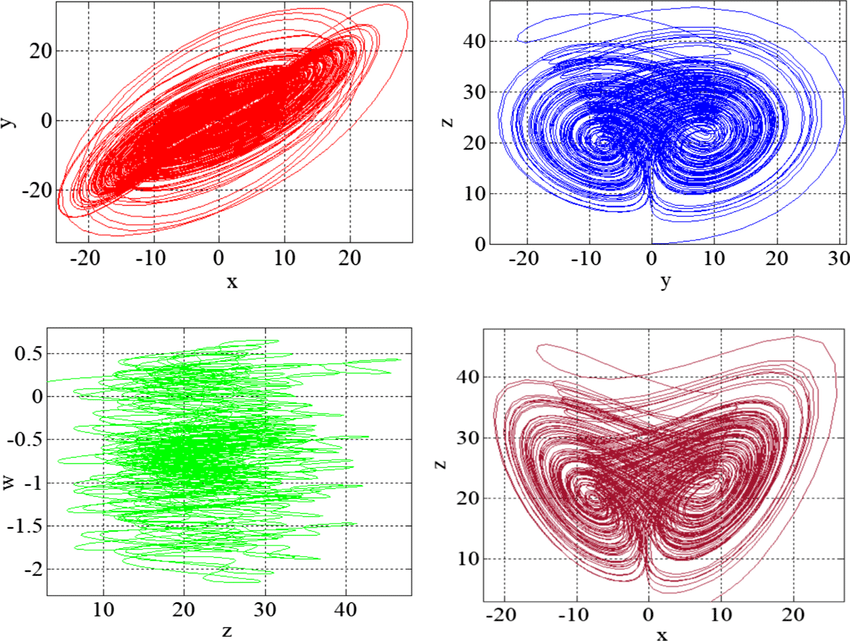
Multistability Analysis and Function Projective Synchronization in Relay Coupled Oscillators
Regions of stability phases discovered in a general class of Genesio-Tesi chaotic oscillators are proposed. In a relatively large region of two-parameter space, the system has coexisting point attractors and limit cycles. The variation of two parameters is used to characterize the multistability by plotting the isospike diagrams for two nonsymmetric initial conditions. The parameters window in which the jerk system exhibits the unusual and striking feature of multiple attractors (e.g., coexistence of six disconnected periodic chaotic attractors and three-point attraction) is investigated. The
Design of Positive, Negative, and Alternating Sign Generalized Logistic Maps
The discrete logistic map is one of the most famous discrete chaotic maps which has widely spread applications. This paper investigates a set of four generalized logistic maps where the conventional map is a special case. The proposed maps have extra degrees of freedom which provide different chaotic characteristics and increase the design flexibility required for many applications such as quantitative financial modeling. Based on the maximum chaotic range of the output, the proposed maps can be classified as positive logistic map, mostly positive logistic map, negative logistic map, and
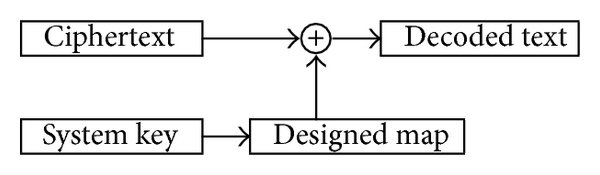
Trajectory control and image encryption using affine transformation of lorenz system
This paper presents a generalization of chaotic systems using two-dimensional affine transformations with six introduced parameters to achieve scaling, reflection, rotation, translation and/or shearing. Hence, the location of the strange attractor in space can be controlled without changing its chaotic dynamics. In addition, the embedded parameters enhance the randomness and sensitivity of the system and control its response. This approach overpasses performing the transformations as post-processing stages by applying them on the resulting time series. Trajectory control through dynamic
New hybrid synchronisation schemes based on coexistence of various types of synchronisation between master-slave hyperchaotic systems
In this paper, we present new approaches to study the co-existence of some types of synchronisation between hyperchaotic dynamical systems. The paper first analyses, based on stability theory of linear continuous-Time systems, the co-existence of the projective synchronisation (PS), the function projective synchronisation (FPS), the full state hybrid function projective synchronisation (FSHFPS) and the generalised synchronisation (GS) between general master and slave hyperchaotic systems. Successively, using Lyapunov stability theory, the coexistence of three different synchronisation types is
Keys through ARQ: Theory and practice
This paper develops a novel framework for sharing secret keys using the Automatic Repeat reQuest (ARQ) protocol. We first characterize the underlying information theoretic limits, under different assumptions on the channel spatial and temporal correlation function. Our analysis reveals a novel role of dumb antennas in overcoming the negative impact of spatial correlation on the achievable secrecy rates. We further develop an adaptive rate allocation policy, which achieves higher secrecy rates in temporally correlated channels, and explicit constructions for ARQ secrecy coding that enjoy low
Pagination
- Page 1
- Next page ››
